ZK-SNARKs vs. ZK-STARKs: A Detailed Cryptographic Comparison
Zero-knowledge proofs (ZKPs) are revolutionizing the blockchain world, offering a way to prove knowledge without revealing it. Two leading paradigms—ZK-SNARKs and ZK-STARKs—approach this goal in very different ways.
This comprehensive comparison helps developers, architects, and researchers understand which technology fits their specific use case, covering performance metrics, security assumptions, trust models, and real-world deployment patterns.
Fundamental Differences at a Glance
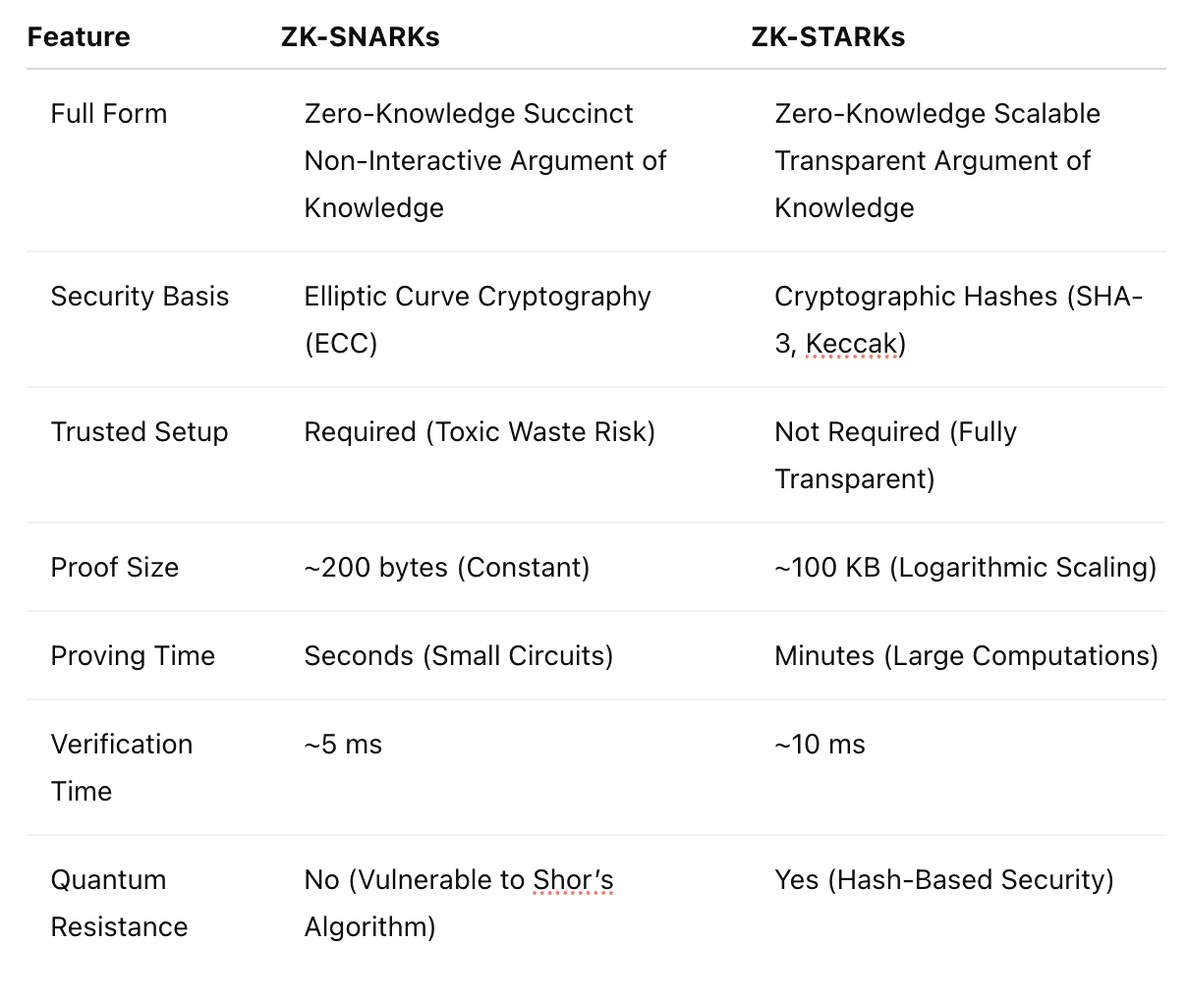
Comparison of core characteristics between ZK-SNARKs and ZK-STARKs
ZK-SNARKs
Succinct Non-Interactive ARguments of Knowledge - Focus on proof succinctness and verification speed.
- Proof Size: Constant (~288 bytes)
- Verification: Fast (~10ms)
- Trust Setup: Required (trusted setup ceremony)
- Quantum Resistance: No (relies on elliptic curves)
- Prover Time: Moderate to high
ZK-STARKs
Scalable Transparent ARguments of Knowledge - Focus on transparency and scalability without trusted setup.
- Proof Size: Larger (~100-200KB)
- Verification: Moderate (~100ms)
- Trust Setup: Transparent (no trusted setup)
- Quantum Resistance: Yes (hash-based cryptography)
- Prover Time: Higher (but better scaling)
Cryptographic Foundations: How They Work
ZK-SNARKs: Algebraic Magic with Pairings
SNARKs encode computation as polynomial equations and use elliptic curve pairings for efficient verification.
Core Technical Components:
- R1CS (Rank-1 Constraint System): Converts program logic into algebraic constraints A·B = C
- QAP (Quadratic Arithmetic Program): Transforms constraints into polynomial form for evaluation
- Elliptic Curve Pairings: Enables succinct verification using curves like BLS12-381 or BN254
- Common Reference String (CRS): Generated during trusted setup, used for proof generation and verification
- Proof Systems: Groth16 (circuit-specific), PLONK (universal), Marlin, Halo2
How It Works:
- Program compiled to arithmetic circuit
- Circuit constraints converted to R1CS format
- R1CS transformed to polynomial equations (QAP)
- Prover generates proof using CRS and witness values
- Verifier checks proof using CRS and public inputs
ZK-STARKs: Hash-Based & Transparent
STARKs use hash-based cryptography and interactive oracle proofs, eliminating the need for trusted setup.
Core Technical Components:
- AIR (Algebraic Intermediate Representation): Describes computation as state transition constraints
- FRI (Fast Reed-Solomon IOP): Proves low-degree polynomiality using Merkle trees
- Merkle Trees: Hash-based commitment scheme for polynomial evaluations
- Rescue/Poseidon Hashes: ZK-friendly hash functions used in constraint systems
- No Trusted Setup: Fully transparent protocol with no toxic waste
How It Works:
- Program expressed as computational trace in AIR
- Trace encoded as low-degree polynomials
- Polynomial evaluations committed via Merkle tree
- FRI protocol proves polynomial low-degree
- Verifier samples random points for verification
Performance & Scalability: Which is Faster?
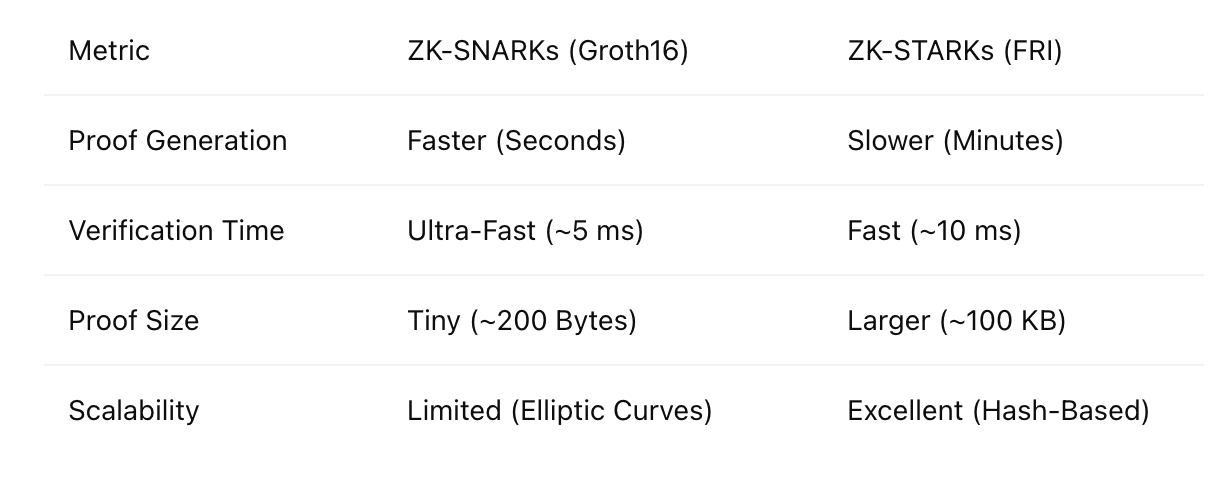
Performance comparison across different metrics and use cases
Why the Performance Differences?
ZK-SNARKs Performance Profile
- Small Proof Sizes: Elliptic curve pairings enable constant-size proofs (~288 bytes)
- Fast Verification: Pairing operations are efficient (~10ms verification time)
- Prover Overhead: High due to complex elliptic curve operations
- Memory Intensive: Large circuits require significant RAM
- Circuit-Specific Optimization: Groth16 requires circuit-specific setup but offers best performance
ZK-STARKs Performance Profile
- Larger Proof Sizes: Hash-based proofs scale logarithmically (~100-200KB)
- Verification Trade-off: Moderate verification time but scales better with circuit size
- Prover Scalability: Better parallelization and scaling for large circuits
- Memory Efficient: Lower memory requirements for large computations
- Transparent Setup: No trusted setup overhead or ceremony requirements
| Metric | ZK-SNARKs | ZK-STARKs | Implications |
|---|---|---|---|
| Proof Size | Constant (~288 bytes) | Logarithmic (~100-200KB) | SNARKs better for on-chain storage, STARKs better for large computations |
| Verification Time | ~10ms | ~100ms | SNARKs win for high-frequency verification |
| Prover Time | High (scales with circuit) | High but better scaling | STARKs scale better for very large circuits |
| Memory Usage | High for large circuits | More efficient for large circuits | STARKs better for memory-constrained environments |
| Setup Time | Complex trusted setup | No setup needed | STARKs eliminate ceremony overhead |
Security & Trust Assumptions
ZK-SNARKs: The "Toxic Waste" Problem
SNARKs require a trusted setup ceremony where secret parameters are generated. If these parameters are compromised, an attacker could generate fake proofs.
Security Concerns
- Toxic Waste: Secret parameters that must be destroyed after setup
- Single Point of Failure: Compromised setup breaks all proofs
- Quantum Vulnerable: Elliptic curve cryptography is not quantum-safe
- Implementation Risks: Complex math increases implementation error risk
Mitigation Strategies
- MPC Ceremonies: Multi-party computation setups (e.g., Zcash's Powers of Tau) where trust is distributed
- Universal Setups: Used in PLONK and Marlin—one setup works for all circuits up to a maximum size
- Updatable Setups: Systems where new participants can join and update the setup over time
- Formal Verification: Mathematical verification of implementation correctness
ZK-STARKs: Transparent and Post-Quantum
STARKs eliminate trusted setup entirely, relying on cryptographic hash functions that are transparent and quantum-resistant.
Security Advantages
- No Trusted Setup: Eliminates toxic waste and ceremony risks
- Post-Quantum Security: Based on hash functions resistant to quantum attacks
- Transparency: All parameters are public and verifiable
- Information-Theoretic Security: Security based on information theory rather than computational hardness
Technical Foundation
- Hash-Based Cryptography: Relies on hash functions like Keccak, Rescue, Poseidon
- Interactive Oracle Proofs: FRI protocol provides soundness guarantees
- Merkle Tree Commitments: Provides binding and hiding properties
- Error-Correcting Codes: Reed-Solomon codes ensure robustness against malicious provers
Real-World Applications
Where ZK-SNARKs Shine
Privacy-Preserving Blockchains
Zcash, Aztec Network
- On-chain shielded pools
- Groth16-based proof systems
- Relayers manage anonymity sets
- Small proof sizes ideal for blockchain
Ethereum zkRollups
zkSync, Scroll, Polygon zkEVM
- zk circuit-based transaction validation
- Recursive proof aggregation
- Verified on Ethereum L1
- Fast verification critical for UX
Mobile Light Clients
Celo, Mina Protocol
- Small SNARK proofs in mobile wallets
- Validate chain state without full nodes
- Low bandwidth requirements
- Battery-efficient verification
Where ZK-STARKs Excel
Post-Quantum Secure Chains
StarkNet, Manta Network
- Cairo VM (custom zkVM)
- STARK proofs with no trusted setup
- Submitted via StarkWare's verifier contract
- Future-proof quantum resistance
High-Throughput zkRollups
StarkEx (dYdX, Sorare, Immutable)
- Centralized sequencer builds batches
- Prover generates STARK proofs
- Verifier contract checks state root
- Scales to 100,000+ TPS
General-Purpose zkVMs
Polygon Miden, RISC Zero, zkWasm
- AIR + FRI over WebAssembly
- Scalable general-purpose zk circuits
- Support for arbitrary computation
- Better scaling for complex logic
Future Trends & Hybrid Approaches
Recursive Proofs
SNARK Recursion
- Nova: Incrementally verifiable computation
- Halo2: Recursive proof aggregation
- Plonky2: Combining PLONK with FRI
- Use Case: L2->L1 proof aggregation
STARK Recursion
- Fractal: Recursive composition of STARKs
- Recursion in AIR: Native support for recursive proofs
- StarkNet's SHARP: Shared prover for proof aggregation
- Use Case: Cross-chain state verification
Proof Aggregation
Both paradigms are exploring proof aggregation to reduce on-chain verification costs:
- Batch Verification: Verify multiple proofs simultaneously
- Proof of Proofs: Aggregate many proofs into a single proof
- Layered Systems: Use STARKs for computation, SNARKs for final verification
- Multi-Prover Networks: Distributed proving networks for scalability
zkEVMs vs zkVMs
SNARK-based zkEVMs
Scroll, Taiko, Polygon Hermez
- Full EVM bytecode compatibility
- Concise proof generation
- Existing toolchain integration
- Faster time-to-market
- Challenges: Proving overhead, gas costs
STARK-based zkVMs
Cairo VM, Polygon Miden, RISC Zero
- General-purpose virtual machines
- Long-term scalability advantages
- Post-quantum security ready
- Better parallelization
- Challenges: Larger proofs, ecosystem maturity
Which One Should You Choose?

Decision flowchart for selecting between ZK-SNARKs and ZK-STARKs based on project requirements
| Requirement | Choose ZK-SNARKs If... | Choose ZK-STARKs If... |
|---|---|---|
| Proof Size Critical | ✅ On-chain storage limited, need constant-sized proofs | ❌ Proofs can be larger (100-200KB acceptable) |
| Verification Speed | ✅ Need sub-10ms verification time | ❌ 100ms verification time acceptable |
| Trust Model | ❌ Comfortable with trusted setup or MPC ceremonies | ✅ Need fully transparent, trustless setup |
| Quantum Resistance | ❌ Not concerned about quantum threats | ✅ Future-proof quantum resistance required |
| Circuit Complexity | ✅ Circuits are moderate size (under 1M constraints) | ✅ Circuits are very large (millions of constraints) |
| Ecosystem Maturity | ✅ Need mature tools and existing integrations | ❌ Can work with newer, evolving toolchains |
| Prover Resources | ✅ Have access to powerful servers with GPUs | ✅ Can handle memory-intensive proving |
Final Verdict: The Battle Isn't Over
Current Reality: ZK-SNARKs Dominate
- Mature tooling and developer ecosystems
- Proven production deployments (Zcash, zkSync, Scroll)
- Small proof sizes ideal for blockchain constraints
- Established security track record
- Better integration with existing EVM infrastructure
Choose SNARKs for: Production deployments today, EVM compatibility, minimal on-chain footprint.
Future Direction: ZK-STARKs Rising
- Transparent setup eliminates trust assumptions
- Post-quantum security ready for long-term protection
- Better scalability for massive computations
- Growing toolchain and community support
- Innovation in general-purpose zkVMs
Choose STARKs for: Future-proof applications, quantum resistance, complex computations, trust minimization.
The Winning Strategy: Hybrid Approaches
In many cases, the optimal solution combines both technologies:
STARKs for Computation
Use STARKs for transparent, scalable proving of complex computations
SNARKs for Verification
Use SNARKs to create succinct final proofs for on-chain verification
Recursive Composition
Layer systems where STARKs prove batches, SNARKs prove aggregated results
The convergence of ZK-SNARKs and ZK-STARKs will likely define the next generation of privacy-preserving and scalable blockchain infrastructure. Rather than choosing one over the other, forward-looking projects are exploring how to leverage the strengths of both paradigms.
